Validate input from all sources!
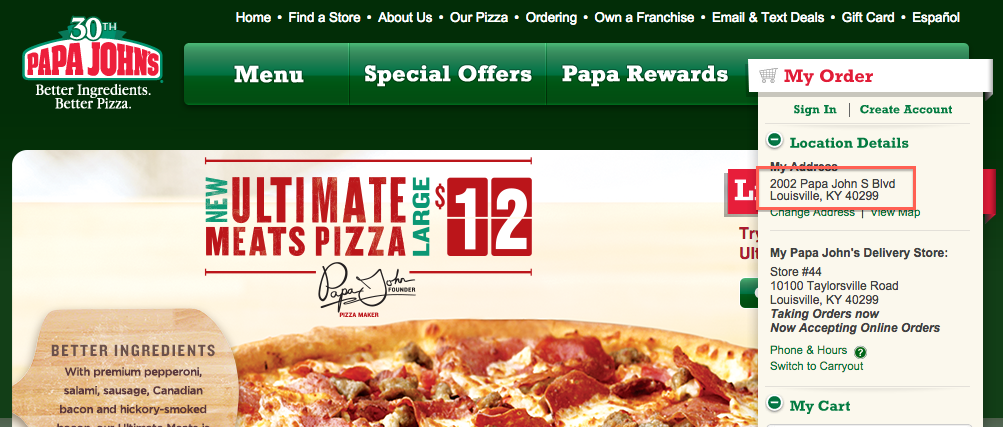
What caught my eye was address information that is not pulled from a backend database:
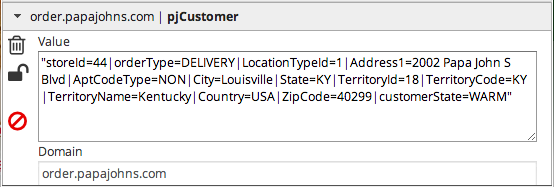
Values are stored in the “pjCustomer” cookie, not encrypted, right there for you (or another device user) to read:
The server does not handle tampered input well–specifically opening and closing script tags:
Maybe data stored in this cookie is not validated here because it was set by the server in an earlier web page when a visitor first inputs address information. There the server does a lookup to ensure it is a real address. Once the server validates the address, it locates the closest store and proceeds through the workflow. Perhaps at this point it is assumed that pjCustomer data is safe.
Like other input sources, data stored in cookies should be checked for tampering: https://www.owasp.org/index.php/Data_Validation#Prevent_parameter_tampering
CWE-472: External Control of Assumed-Immutable Web Parameter: http://cwe.mitre.org/data/definitions/472.html